Cyber Security Courses
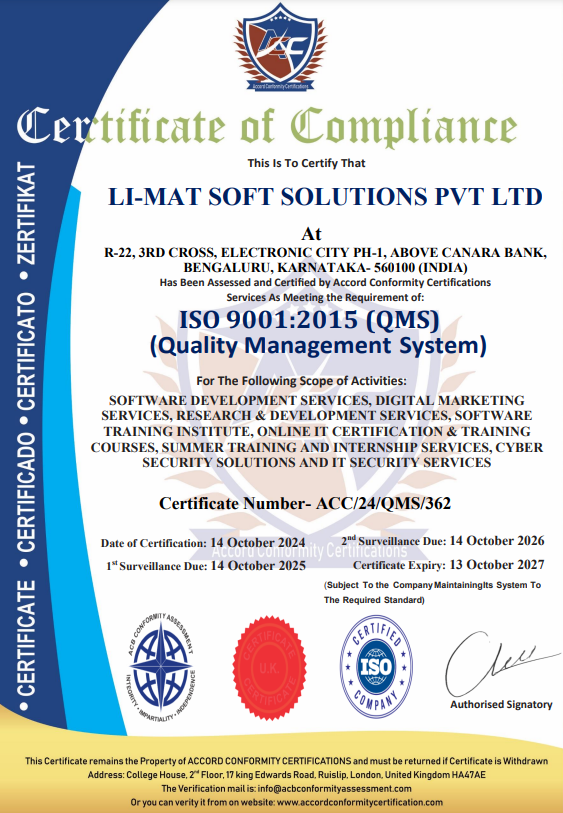
with Certificates
IT TRAININGS & DEVELOPMENT
Learn Cybersecurity concepts like Cryptography, Hijacking, SQL Injection, Penetration Testing, Hacking, Vulnerability, and Protection..
Registered Office : Bangalore
Branch : Kanpur
Expert-led interactive sessions.
60+ hours of dedicated learning.
Key projects and Certifications.
WhatsApp Support Group.